|
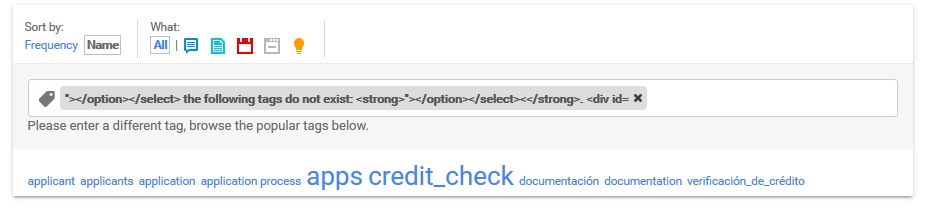
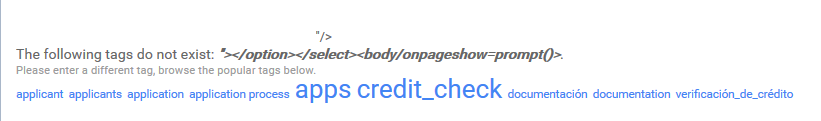
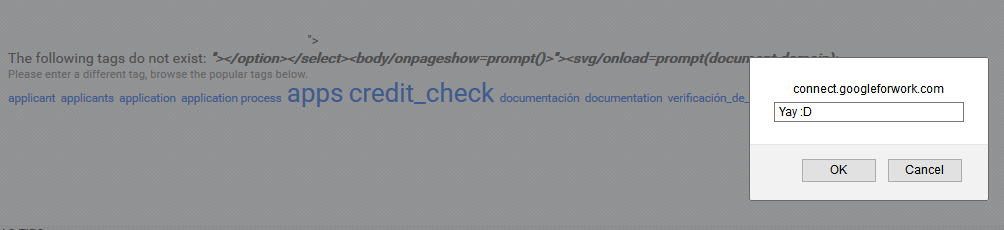
Jive is software created by Jive Software which allows companies to roll out communities for either collaboration between partners and employees or customer service for customers. Many companies such as Google, Apple and Oracle have installations of Jive so the potential impact of finding a vulnerability in Jive is quite large. Vulnerability DiscoveryI started the vulnerability discovery journey by looking for vulnerabilities in Google's web applications. I was made aware of the domain googleforwork.com after reading the following article by @soaj1664ashar. This article peaked my curiosity so I went looking. The web application on the domain I was looking at is located on connect.googleforwork.com which is Google's installation of Jive which is something I did not realise until I actually found the vulnerability. Following my penetration testing procedure I started off by looking at webpages that unauthenticated users can see and it wasn't long until I landed on the following webpage - https://connect.googleforwork.com/community/applicants/apps/english/credit-check/tags?tags=example This page immediately stood out since the parameter "tags" was passing it's value directly into the source without any santisation so we had our first reflection. Identifying this reflection usually involves checking the source code and seeing how it handles special characters but thanks to an innovative tool created by @brutelogic for @brutalsecrets subscribers I could confirm the reflection in a matter of seconds. I began with some basic vectors but had no luck, the vectors were just reflected as a normal tag would be so I tried some more abnormal tags and with the following "></option></select>< I got - Well, that's odd isn't it?! Some of the source was now being reflected back in the tag so I just knew I was a step closer. Simply adding a vector that renders a prompt box after the current "></option></select>< did not work but while trying to get it to work I discovered the addition of <body/onpageshow=prompt()> broke me right out of the tag box. Seeing this obviously made me grin ear to ear and adding one of my favourite vectors to the end of this gave us the one and only prompt box! Vulnerability ImpactAfter getting super excited and sending a report to Google's security team I soon learnt that this web application was third party (Google's security report form actually tells you) but reports are obviously still of interest to Google so I sent the report and it was triaged shortly after. After the initial disappointment wore off I thought to myself that if it's third party and used by Google lots of other companies must use it. I was right. Using Google hacking I soon found many other popular companies that were vulnerable to the same bug, even Jive Software themselves! Here was just some of the vulnerable domains - After identifying the company responsible for the software was Jive Software I immediately contacted them as well as each individual company in case they wanted to patch much sooner which a lot did. Some patched so quick in fact they weren't vulnerable at the time I created this post but I did manage to submit them to Open Bug Bounty beforehand. Some of the domains that were quickly patched (click on them to see OBB reports) include T-Mobile, Oracle, American Express, Activision, AMD, Shaw, RSA, HPE and Checkpoint. Vulnerability Timeline11th of April 2016 - Vulnerability Discovered 11th of April 2016 - Vulnerability report sent to Jive Software 11th of April 2016 - Vulnerability report sent to affected companies 13th of April 2016 - Vulnerability acknowledged by Jive Software 19th of April 2016 - Patch released by Jive Software I'd like to thank @soaj1664ashar for the blog post he created which enabled me to discover Google's installation of Jive and @brutelogic for his tool available to @brutalsecrets subscribers which allowed me to confirm the parameter reflection and encouraged me to dig deeper into that specific parameter.
Cameron Dawe, Spam404 Founder
1 Comment
At Spam404 we are always looking for new ways to help protect internet users from scams and other abusive content found online. This is exactly why we have created an anti-scam filter which can be used with AdBlock and Adblock Plus, two very popular browser extensions.
We have integrated the data we hold on websites created to scam into this filter to make browsing the internet a much more safer experience. Our filter is completely free and so is AdBlock or Adblock Plus! Here is how to subscribe to our anti-scam filter: 1. Install AdBlock or Adblock Plus. 2. Go here and under "Miscellaneous" you can find our anti-scam filter and to subscribe just click "Spam404" next to "Subscribe:". It's as simple as that! If you find a suspected scam website that isn't blocked by our filter please report the website here. If you have any questions, comments or even criticism about our anti-scam filter please feel free to leave them below as a comment, we look forward to hearing from you! Cameron Dawe, Spam404 Founder Some of you will know that Spam404 has a very active blacklist and recently many popular services have integrated our very own blacklist so we thought a post updating you about the services which use our blacklist is necessary.
Our blacklist has had a primary focus since the beginning of our first listing. Our primary focus was to list the websites that are offering things for free after the user completes an offer but after the offer the user soon finds out it was just a scam and the thing they're supposed to get for free was to encourage the user to complete the offer. We noticed that websites hosting these scams are not actively blacklisted and therefore we made it our aim to blacklist as many of these abusive websites as possible to allow internet users to be aware of the scams. The first service to begin using our blacklist was URLVoid.com. URLVoid is a very popular website reputation service which empowers internet users to check a websites reputation before they access the website. Upon finding URLVoid we immediately agreed that it would be perfect for our blacklist to be used by the service to alert internet users of abusive websites that we list. You can find Spam404 on the "About Us" page. The same company behind URLVoid also own and operate ScamVoid.com. ScamVoid is a very similar service in a sense that abusive websites can be found using ScamVoid's domain search but we believed the nature of the websites we blacklist would also be important to be on ScamVoid. Just this week we got in contact with Web of Trust which is undoubtedly the largest website reputation service on the internet and we felt it very important for such a service to use our blacklist. We are pleased to announce that Web of Trust now use our blacklist as a third party source. An example of our blacklist being used on Web of Trust can be found here. We are currently in talks with other services so we will ensure to keep you updated if any other awesome services use our blacklist. Spam404 Administration Team Welcome to the new Spam404 Blog. We have decided to start our blog to give you guys a much better understanding of what we are up to and to also allow another way to contact us via the comments of each post.
On our blog we plan to regularly post what we are up to which could be new features added to Spam404 or even investigations we are currently carrying out against abusive content creators on the internet. We would like to use this blog post to also thank everyone that has sent us abusive content since our launch and we can report that Spam404 has helped remove over 5000 articles of abusive content from the internet for good. Our traffic per day is also growing so we thank you if you have told any of your friends or family about us! We feel the need to also tell you guys about our Twitter which we recently created and our Twitter profile is currently our preferred method of contact. Our Twitter profile also allows you the opportunity to privately message us through Twitter's Direct Messaging system but remember to ask us to follow you beforehand! Spam404 Administration Team |
BlogHere is the Spam404 Blog. We will post news, investigations and anything else we are up to! Archives
June 2016
Topics
All
|
|
© 2013 - 2023 Spam404. All Rights Reserved.
|

 RSS Feed
RSS Feed